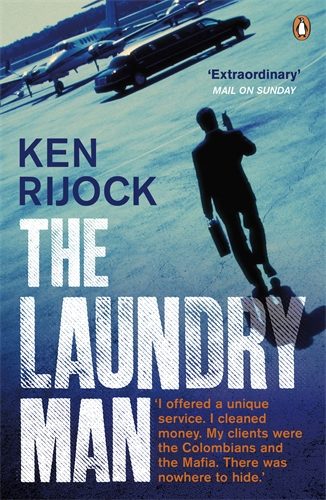
 In this article, first published in the Whistleblower Edition of TJN’s newsletter, Tax Justice Focus, convicted money launderer Kenneth Rijock (author of The Laundry Man, Penguin, 2013) offers some practical advice to those who might be considering blowing the whistle on their employers. Helpful tip: get yourself a good lawyer.
In this article, first published in the Whistleblower Edition of TJN’s newsletter, Tax Justice Focus, convicted money launderer Kenneth Rijock (author of The Laundry Man, Penguin, 2013) offers some practical advice to those who might be considering blowing the whistle on their employers. Helpful tip: get yourself a good lawyer.
Although my primary field is the identification and detection of financial crime in general, with an emphasis on money laundering, I often find myself in the role of working with whistle-blowers, when reporting on white-collar crime in progress, where the information is received from a confidential source. Inasmuch I have substantial experience in conducting operations under the radar, when I was involved in activities that I wanted to remain confidential, I am offering these suggestions for whistle-blowers who also wish to quietly collect material, without attracting unwanted attention from the target of their inquiries. They are what we refer to as operational security.
Given the propensity of many whistle-blowers’ targets, especially when they are large entities, to maintain agents to investigate unhappy employees, as potential whistle-blowers, it is prudent to take a number of measures that will: (1) keep your information secure, (2) protect the identities of your sub-sources, and (s) prevent you from being a civil, or even, criminal, defendant as the result of your actions.
First of all, you must assume that all your means of electronic communication is potentially under surveillance. This includes telephone calls from your land-line or mobile telephones, and your known email addresses. You need to adopt what is in essence the tradecraft of espionage if you want to avoid interception of your communications with media, or your sub-sources.
This means never using your present email addresses; some whistle-blowers utilize obscure email providers, from faraway jurisdictions, and using them only for short periods, In conjunction with the same activity on the other end ( your own sources),
And both parties using Internet cafes, libraries, public wifi resources, alternating them, to avoid any pattern. Some people use Hushmail (www.hushmail.com) a free, encrypted email service, changing their address & password frequently, to avoid detection.
Both sender and recipient have the address AND password, for there is only a need for one account. Here’s why:
Since all emails, even when deleted by the sender or recipient, remain available to prying eyes, prepare drafts only; the recipient himself or herself deletes the draft when read. Both parties regularly monitor the single account, looking for messages from the other. Drafts are not saved anywhere, because they technically are never sent or received. This technique ensures that your messages cannot be read by others, unless they know what you are doing, and look for drafts, but they need to have your address & password, and know what to look for.
The second measure I recommend is to never, in writing, identify your sources by name; designate an alias, or code word, so that their identity is always protected in your notes and documents, and under no circumstances do you ever put his telephone number down anywhere near that code name.; keep his telephone number and the email address in a totally different file, hard copy only, so that it appears to be that of another contact, client, vendor, or other innocent party.
You obviously will need to compose memoranda, type up your handwritten notes, and the progress of your investigation. Do not use any of the computers or devices that are connected to the Internet, for this purpose. Obtain an inexpensive laptop, new. and use it exclusively for your whistle-blower project. It is to have its wifi capability completely and permanently disabled, and with no USB or hard-wired connection to the World Wide Web. This is known as a stand-alone computer; it is not ever to be networked with any other system, to guarantee that it cannot be accessed remotely, and that it will never be the target of an intrusion, worm, or hack.
If you must install programs, such as MS Word, or Excel, do so from a CD, never install anything from the Internet, not even from one of your other computers, for that may already been compromised. Do not ever leave this computer out where it can be seen; store it in a very unlikely place, so that anyone who breaks in will not find it. If you follow these suggestions, then it is highly unlikely that any company investigator will learn the identity of your sources
The third issue is protecting oneself from civil suits, and also from possible criminal prosecution. The information contained in this article is not intended to be legal advice, and you are strongly advised to consult with a competent attorney, who is familiar with not just libel and slander issues, but also with trade secrets, classified information laws, and the corporate culture of the type of entity that you plan to publicly expose, or blow your whistle to government or law enforcement.
You may not be aware of all the legal ramifications of your activities, and you should fully understand the potential legal risks, both now, and in the future, so be sure to consult a good lawyer before engaging in your whistle-blowing campaign, for some of what you are planning could cross the line into either an illegal act, or be grounds for a civil suit. Understand the risks before you jump into your project.
That being said, you are encouraged to dig, probe and poke around any issue, where you believe that there are facts that must be extracted, and to take any damaging information that you find to the appropriate regulator, or agency, or media, where it will get the attention it deserves.
Good luck.
Related articles

Finally, the European Court of Justice cracks down on trusts

Financial secrecy has entered the EU AML rulebook. What comes next?

Malta: the EU’s secret tax sieve
The tax justice stories that defined 2025

2025: The year tax justice became part of the world’s problem-solving infrastructure

‘Illicit financial flows as a definition is the elephant in the room’ — India at the UN tax negotiations
Tackling Profit Shifting in the Oil and Gas Sector for a Just Transition

Follow the money: Rethinking geographical risk assessment in money laundering
Democracy, Natural Resources, and the use of Tax Havens by Firms in Emerging Markets